Dateline Washington, D.C. – Finals of the U.S. regional Patty Cake Olympics were held recently in the nation’s capitol. An eclectic and diverse group of contestants demonstrated hand/eye coordination with creative skills as they slapped each other to meaningless victory.
The competition is scored on poise, precision and originality. Each participant must recite some version of the nursery rhyme while clapping in time with the song.

Vice President Kamala Harris placed second in the competition, losing points for her chopped up, masticated word salad interpretation of this beloved children’s classic:
Patty cake, Patty cake, baker’s person,
Bake me a cake as fast as (insert preferred pronoun here)
have the ability to see what can be unburdened by what has been and then to make the possible actually happen;
Roll it, pat it every day, it is time for us to agree that
It’s time for us to do what we have been doing,
and that time is every day to mark it with a B,
And put it in the oven for unviable tissue mass and me.
And the winner is…
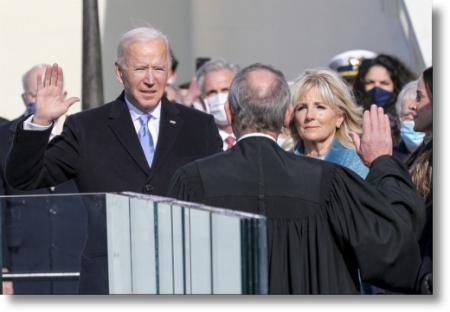
President Joe Biden!
Although Mr. Biden mumbled and bumbled his way through a traditional rendition of the lyrics, the judges were impressed with Joe’s ability to distinguish his right hand from his left with more than a fifty percent degree of accuracy, giving him a total of ten votes even though the panel consists of only six judges. White house press secretary Karine Jean-Pierre hailed the win as “the greatest achievement of the Biden presidency thus far.”
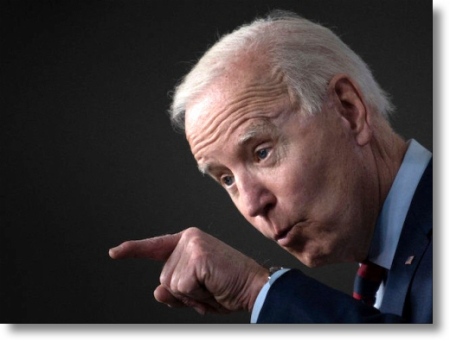
The leader of the free world was also on hand for the World Pull-My-Finger Championships.
Participants must convince one of the six judges to “pull my finger.” Judges then catalog the gaseous anomalies based on four intense criteria: odor, volume, decibel levels and wetness. The event is by invitation only.

Notably absent from this year’s festivities was previous winner Mrs. Barack Hussein Obama. The former First Lady could not attend due to a repetitive brain stress disorder suffered when she used the word racist way too many times in a single sentence. Twice. Mrs. Obama is expected to make a full recovery.

Likewise unable to attend was five-time Grandmaster Arnold Schwarzenegger. The Austrian born actor was busy planning an invasion of Poland. “Screw their freedom, too.” quipped the Terminator star, “I’ll teach them to obey traffic light laws!” The former California Republican Governor was also engaged in post-production work on his latest film, a science-fiction comedy/spoof about two non-English speaking classical composers who time travel to early 1950’s New York City and accidentally invent Rock ‘N’ Roll. Co-staring John Cleese as near-deaf Ludwig van Beethoven, Bach to the Future is scheduled for release late next year.
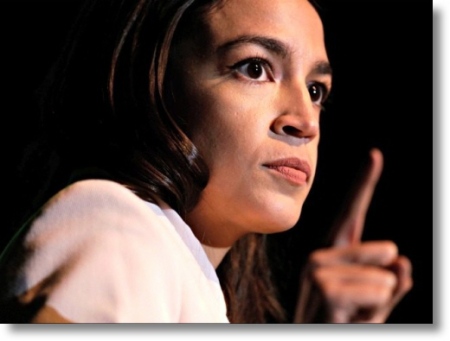
U.S. House of Representatives member Alexandria Ocasio-Cortez (D-NY) declined an invitation to compete claiming, “My farts don’t stink.” However, reliable sources closest to Ms. Ocasio-Cortez’s backside have informed us that “AOC’s ass gas could strip paint.”
Proceedings slowed to a snail’s pace when celebrity guest judge Greta Thunberg stood up and proclaimed “how dare you,” before launching into a 20-minute oration concerning a link between methane and global warming every time a finger was pulled.
The judges could not declare a victor at this time, as they are all currently being treated for oxygen deprivation at the George Washington University Hospital. Officiants expect to announce the winner’s name by the end of the year.
____________________
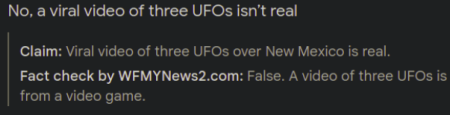
Disclaimer: Fake news!
The preceding article is a work of fiction.
All incidents are the product of the author’s deranged imagination.
Any resemblance to actual events, places or persons, living or dead, was purely irresistible.